Kasm + UmbrellaNET Hybrid Workspace
Secure, Compliant Cloud Workspaces
Most remote access models rely on broad trust and loose control. VPNs extend access too far. Endpoint-based access pushes data to devices you do not control.
Kasm and UmbrellaNET change how access is delivered. Workspaces run inside controlled environments, not on user devices. Access is contained and enforced.
Why UmbrellaHUB
Control. Containment. Delivered.
Most remote access models rely on trust that is too broad and control that is too loose. VPNs extend network access further than they should. Endpoint-based access pushes applications and data handling out to devices you do not control. Legacy VDI adds complexity without resolving how access is actually enforced.
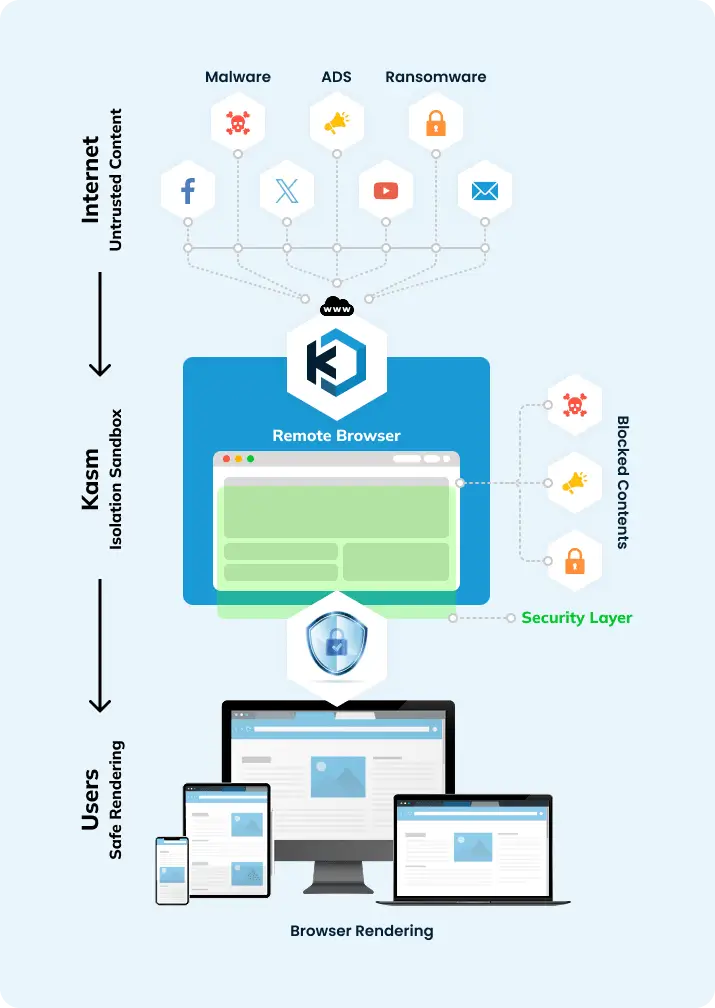
UmbrellaHUB changes how access operates. Kasm and UmbrellaNET work together as a single workspace model. Kasm provides containerised workspace delivery. UmbrellaNET provides the infrastructure, control model, and operational enforcement. Access is not extended. It is contained. Workspaces run inside controlled environments where behaviour, data handling, and access are governed by policy, not assumed trust.
Users can operate across office, remote, offshore, and hybrid settings, but access remains restricted to what is defined and enforced. Nothing runs locally unless explicitly allowed. Data does not move freely between systems, devices, or locations. Sessions operate inside the environment, not on the endpoint.
This removes endpoint risk, limits exposure, and gives the business a controlled way to deliver access without relying on devices, networks, or user behaviour to enforce control.
Why It Works
Launch. Isolate. Control.
When a user connects, Kasm launches a secure, isolated container running a browser, desktop, or application. That session runs in the cloud inside UmbrellaNET infrastructure, not on the user’s device.
The session is streamed to the browser as pixel data. Nothing runs locally. Files are not downloaded unless policy allows it. Sessions can be disposable or persistent depending on operational requirements. When the session ends, the container can be wiped clean or retained under defined control.
Applications remain separated from the endpoint. Data stays inside the environment. User activity is contained within the session, reducing exposure and limiting movement across systems.
Kasm delivers the containerised workspace layer. UmbrellaNET defines how it is deployed, controlled, and operated as part of a Hybrid Workspace model built for secure, scalable access.
Industry Use Cases
UmbrellaHUB provides a central way to manage secure cloud desktops and browser workspaces across different teams and operating environments.
UmbrellaNET’s hybrid workspace model adapts to how access needs to be controlled, aligned to compliance requirements, user types, and operational conditions.
Here’s where it delivers real results:
How It Works
Session. Isolation. Control.
Deployment Options
| Deployment Type | Description | |
|---|---|---|
| Hosted by UmbrellaNET | Deployed and managed entirely by UmbrellaNET in our Tier 4 sovereign cloud | |
| Hybrid Deployment | Hosted on your infrastructure with support, monitoring, and provisioning by UmbrellaNET | |
| Self-Managed |
|
Compliance
Defined. Enforced. Auditable.
Deployments are aligned to regulated and security-sensitive use cases, including requirements shaped by ISO 27001, NIST, APRA, and broader audit expectations.
Every session operates within defined policy. Access is controlled. Activity is logged. Containers are segmented and isolated by design.
Access is defined, enforced, and auditable. Systems operate within policy, not outside of it.
Why Clients Choose UmbrellaHUB
Control. Access. Enforcement.
Kasm removes the exposure created by traditional remote access models. Sessions are isolated by default. Access is controlled by policy. Nothing runs locally unless explicitly allowed.
Frequently Asked Questions
Take Control of Access
If your access model relies on extended network trust, unmanaged endpoints, or exposure that sits outside your control, it will continue to create risk.
Most businesses hold onto those models longer than they should.
UmbrellaHUB changes how access is delivered. Workspaces run inside controlled environments. Applications and data stay inside the infrastructure. Access is defined and enforced by policy, not assumed through connection or device.
No extended network access. No reliance on endpoint trust. No exposure that sits outside the environment.
Let’s Start The Conversation
Remote access becomes harder to control as users, devices, and locations expand. Exposure increases. Visibility drops. Weak access models stay in place longer than they should.
If access is not controlled, it will continue to create risk. The model needs to change.
Speak with our team and get a clear path to a controlled, enforceable access model that aligns to how your business operates.
Let’s minimise your risk.